AI in ITAD: Data Security Trends 2026
AI is reshaping IT asset disposition (ITAD), turning it into a key part of cybersecurity strategies.
By 2026, ITAD isn't just about disposing of old hardware - it’s about protecting sensitive data, meeting stricter regulations, and reducing risks tied to modern AI infrastructure. With the average cost of a U.S. data breach now at $10.22 million, businesses can no longer afford outdated methods. AI tools are transforming how companies handle retired hardware, offering faster processes, better accuracy, and stronger compliance.
Key highlights:
- AI-driven data wiping targets complex storage like GPUs and NVMe drives.
- Real-time monitoring ensures secure tracking and anomaly detection.
- Cryptographic proof of destruction replaces outdated paper certificates.
- Predictive tools help manage asset lifecycles and resale value efficiently.
- Regulations like NIST SP 800-88 Rev. 2 demand stricter sanitization methods.
AI-powered ITAD platforms streamline compliance, reduce human error, and maximize recovery value, making them indispensable for modern businesses.
Securis AI Powered IT Asset Tracking
sbb-itb-855056e
AI Improvements in Data Sanitization
AI-driven advancements are reshaping how data sanitization is handled within ITAD processes, enhancing security and efficiency. These technologies are designed to meet stricter regulatory demands while minimizing human error. For example, ITAD platforms now use AI to automatically identify whether a drive is an SSD or HDD and apply the appropriate, standards-compliant wiping method. This ensures compliance on a large scale and supports more streamlined asset management within complex IT environments.
Predictive Sanitization and Asset Lifecycle Management
AI is also playing a key role in predicting when assets should be retired, integrating seamlessly with IT Asset Management (ITAM) systems. By analyzing data, AI models can recommend the best time to retire equipment, allowing companies to group assets efficiently for logistics and pinpoint high-value items - such as GPU-heavy servers - for resale before their value declines. This shift makes ITAD a forward-thinking, data-driven process. As George Ganas from Zones puts it:
"AI is turning ITAD into a proactive, intelligence-led function rather than a reactive one - reducing loss, maximizing recovery, and improving compliance accuracy."
Additionally, automated policies can trigger secure data wiping as soon as an employee leaves, eliminating delays and reducing the risk of errors.
Better Accuracy in Data Wiping and Verification
AI tools enhance accuracy by using visual recognition to quickly identify device models, configurations, and physical conditions. This ensures each device is sanitized according to its specific hardware type and data sensitivity. Real-time monitoring during the sanitization process helps verify accuracy, while automated systems generate audit-ready certificates of destruction. These certificates meet updated standards like NIST SP 800-88 Rev. 2, reducing errors in documentation and providing reliable proof of compliance. This level of automation is especially important as businesses face growing requirements for serialized tracking and reporting on carbon impacts throughout the lifecycle of their hardware.
AI in Chain-of-Custody and Anomaly Detection
As data sanitization processes improve, AI is stepping up to enhance chain-of-custody management and anomaly detection throughout the IT asset lifecycle.
Real-Time Monitoring of Asset Movements
Tracking IT assets as they move between offices, remote workers, and disposal facilities has always been a challenging task. But AI is simplifying this complexity with real-time monitoring and automated alerts that help identify potential issues before they turn into security threats.
AI-powered tools now synchronize serial numbers across multiple databases instantly, eliminating the manual entry errors that often plague traditional tracking methods. For example, when a device arrives at an ITAD facility, AI-driven computer vision systems can immediately identify its model, configuration, and cosmetic condition, removing the need for manual inspections. Linda Li, Chief Strategy Officer of Li-Tong Group, highlights this efficiency:
"At the front end of the process, AI-enabled visual recognition systems identify device models, configurations and cosmetic grades in seconds."
By integrating with HR and IT Asset Management systems, AI also automates ITAD actions when employees leave the organization. This integration provides security teams with real-time updates on which devices are being returned and their exact location within the disposal process. For companies managing thousands of remote workers, this continuous visibility is a game-changer, ensuring that devices stay accounted for and securely handled.
Automated Anomaly Detection
AI doesn’t just track assets - it actively identifies irregularities in ITAD workflows. Advanced platforms can automatically flag missing devices or any deviations from the expected chain-of-custody path. This is particularly valuable for uncovering "unaccounted-for" devices - hardware that shows up in endpoint management tools but can’t be physically located.
AI also plays a critical role in monitoring data wiping and physical destruction processes in real time. Any irregularities or failures are flagged immediately, ensuring complete compliance. For high-value equipment like AI servers with GPUs, AI systems document hardware details and capture photo evidence at every handoff, minimizing the risk of theft. With 95% of business leaders reporting that AI and automation have boosted their security teams’ effectiveness, these advancements are quickly becoming standard in ITAD operations.
Securing Data During AI Infrastructure Decommissioning
With AI advancing the precision of data wiping, new challenges emerge as organizations start decommissioning complex AI hardware. The first wave of GPU-heavy AI servers, initially deployed between 2022 and 2024, is expected to enter decommissioning phases from 2026 to 2029. Experts highlight that AI hardware has become far more intricate and valuable, demanding security protocols that go beyond traditional IT asset disposition (ITAD) practices.
AI infrastructure introduces unique data security concerns. Unlike standard enterprise hardware, GPUs and AI accelerators retain sensitive data in areas such as VRAM, cached model files, system logs, and training datasets - locations that traditional data wiping methods often overlook. Furthermore, by 2026, AI inferencing environments may require power densities as high as 140 kW per rack, alongside specialized liquid cooling systems that must be carefully managed during decommissioning.
Certified Data Erasure for High-Volume Assets
AI-powered tools now enable precise and standards-compliant data erasure, targeting sensitive areas like VRAM and firmware. In AI infrastructure decommissioning, these tools also streamline the identification of dense, complex server configurations for secure processing. Such automation is crucial for managing high-value components like NVIDIA H100 GPUs, which can resell for $25,000–$40,000, and A100 GPUs, valued at $4,600–$15,000.
Modern sanitization processes ensure the complete erasure of VRAM, cached model files, and firmware data. Robotics play a key role in securely disassembling high-density AI clusters, guaranteeing the elimination of proprietary model weights and intermediate checkpoints stored in VRAM.
Predictive lifecycle planning further enhances security by identifying high-value components for early retirement, reducing the risk of those assets becoming security vulnerabilities. This approach allows organizations to prioritize refurbishment and reuse over bulk destruction, aligning with both security and sustainability goals. Advanced erasure techniques also support the creation of detailed, audit-ready documentation.
Audit-Ready Documentation and Compliance
By 2026, security teams are demanding more than basic destruction certificates - they now require cryptographic proofs of destruction. As George Ganas from Zones explains:
"In 2026, ITAD will become part of the security architecture, not a downstream process... Security teams require cryptographic proof of destruction, not just certificates."
AI platforms streamline compliance by automating audit trail creation, incorporating real-time monitoring and anomaly detection into the chain-of-custody process. Machine learning algorithms identify high-value remarketing opportunities and flag missing assets, ensuring that documentation is accurate and comprehensive. For AI infrastructure, these systems provide detailed logging and data lineage tracking, which are essential for meeting regulatory standards.
Regulations like the California Transparency in Frontier Artificial Intelligence Act (TFAIA) are enforcing stricter oversight of training data handling during decommissioning. Nishant Doshi, CEO of Cyberhaven, underscores this shift:
"By 2026, AI governance will be the top security priority... The leaders will be those who enable productivity while governing every data flow - turning safe AI adoption into a competitive edge."
AI tools also link decommissioning data to Scope 3 emissions reporting and circular economy metrics. This integration allows for the creation of comprehensive ESG optimization reports, modeling the carbon savings and e-waste reduction achieved through reuse over recycling. By aligning security compliance with environmental accountability, organizations can meet both regulatory and sustainability objectives effectively.
Regulatory Compliance and Zero-Trust Security Policies
AI's role in IT asset disposition (ITAD) is expanding, especially as regulations like NIS2, DORA, CSRD, and NIST 800-88 Rev. 2 reshape compliance requirements. By 2026, 77% of stakeholders demand verified proof of compliance - a sharp increase driven by the rising costs of data breaches. As a result, companies can no longer afford to overlook secure asset retirement.
AI platforms are now bringing zero-trust security principles to the disposal phase of storage media. These systems actively monitor and verify the identity and behavior of users and devices interacting with retired assets. If any deviations from expected behavior occur, permissions are revoked automatically. This approach ensures that even end-of-life devices remain secure. Khushboo Kashyap, Senior Director of GRC at Vanta, emphasizes:
"AI adoption can amplify a solid security and compliance program, but it won't fix fundamental gaps".
Generating Verifiable Certificates of Data Destruction
Paper certificates no longer meet the compliance standards of 2026. Instead, AI-powered ITAD platforms now generate cryptographic proof of data destruction, complete with QR codes and secure digital storage. These platforms integrate directly with IT asset management (ITAM) databases to automatically pull details like serial numbers, destruction methods, and timestamps, minimizing the risk of manual errors.
Zero-trust models are also driving a shift toward onsite destruction, ensuring that no data leaves the facility without being properly sanitized. AI-enabled onsite services provide real-time verification and produce serialized certificates tailored to advanced storage technologies like NVMe and self-encrypting drives. Furthermore, privacy laws in states such as Texas, California, Illinois, and Colorado now require detailed documentation of data destruction at the end of retention periods, making AI-generated audit trails essential for legal compliance.
This focus on rigorous certification highlights AI's growing importance in securing ITAD processes.
AI as a Core Component in ITAD Security Strategies
AI significantly reduces the manual workload associated with compliance and security. Machine learning algorithms establish baselines for asset movement and data access, enabling systems to immediately detect and flag unauthorized activities or unusual logins. According to 95% of security leaders, AI and automation have improved the effectiveness of their teams.
By integrating ITAD into broader cybersecurity frameworks, AI simplifies policy enforcement during critical moments like employee offboarding. Automated workflows can simultaneously trigger data destruction and other security measures, minimizing risks from "ghosted" devices. Ignacio Graglia from InvGate explains:
"In 2026, ITAM is becoming a core security and compliance control, providing the visibility needed to identify exposed assets, enforce segmentation policies, and rapidly isolate compromised devices".
With global e-waste expected to hit 82 million metric tonnes by 2030, AI tools also assist in CSRD reporting by tracking carbon savings from asset reuse. These capabilities make AI an indispensable part of modern ITAD strategies.
Comparing Manual vs. AI-Powered ITAD Methods
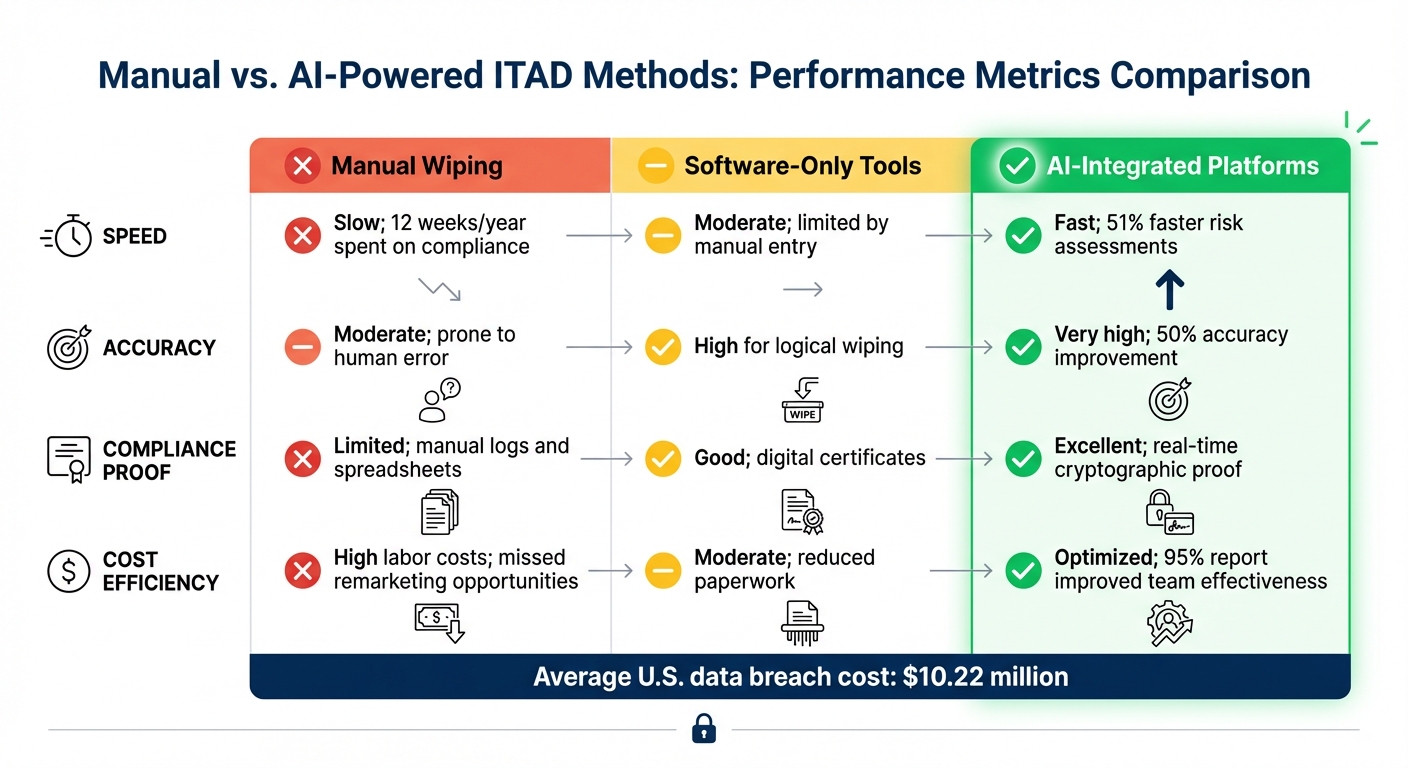
Manual vs AI-Powered ITAD Methods: Speed, Accuracy and Cost Comparison
The evolution of IT asset disposition (ITAD) has taken a sharp turn with the introduction of AI-powered methods. By 2026, the difference between traditional manual approaches and AI-driven systems has become stark. Manual ITAD methods rely on technicians to identify devices, erase data, and document the process - a task that can take several minutes per device and is prone to human error. On the other hand, AI-powered systems, equipped with advanced visual recognition technology, can identify device models, configurations, and cosmetic conditions in mere seconds. (For more on AI's proactive capabilities, see the earlier discussion on predictive sanitization.)
One of the biggest challenges with manual methods is the burden they place on security teams, particularly in documentation and compliance. Teams relying on manual compliance techniques spend an average of 12 weeks annually collecting screenshot-based evidence. Khushboo Kashyap, Senior Director of GRC at Vanta, highlights this inefficiency:
"When teams stop doing manual, screenshot-based evidence collection, they get time back for actual risk reduction".
Cost efficiency is another critical factor. Manual ITAD often prioritizes device shredding to ensure security, which destroys the resale value of high-value components. In contrast, AI-powered platforms use predictive remarketing to determine the best course of action - whether a device should be refurbished, components harvested, or the timing optimized for maximum recovery value. This approach is particularly vital when considering the average cost of a data breach in the United States has reached $10.22 million.
Key Metrics: Speed, Accuracy, and Cost Efficiency
The differences between manual, software-only, and AI-powered ITAD methods are evident when looking at performance metrics. Manual wiping is labor-intensive, with compliance relying on outdated tools like paper logs or spreadsheets. Software-only tools improve digital tracking but still depend on manual inputs, lacking real-time anomaly detection. AI-integrated platforms, however, stand out with speed, accuracy, and advanced compliance features.
| Method | Speed | Accuracy | Compliance Proof | Cost Efficiency |
|---|---|---|---|---|
| Manual Wiping | Slow; 12 weeks/year on compliance | Moderate; prone to human error | Limited; manual logs and spreadsheets | High labor costs; missed remarketing opportunities |
| Software-Only Tools | Moderate; limited by manual entry | High for logical wiping | Good; digital certificates | Moderate; reduced paperwork |
| AI-Integrated Platforms | Fast; 51% faster risk assessments | Very high; 50% accuracy improvement | Excellent; real-time cryptographic proof | Optimized; improved team effectiveness as reported by 95% |
These metrics highlight the transformative impact of AI in ITAD. By reducing human error and streamlining compliance workflows, AI-powered platforms not only mitigate the risk of data breaches but also maximize asset recovery. Beyond traditional data wiping, these platforms automate sanitization across various data storage areas, including VRAM, system logs, and embedded storage, ensuring thorough data erasure during decommissioning.
Companies like Rica Recycling are at the forefront of this transition, combining AI-enhanced ITAD with a commitment to data security, asset optimization, and environmental responsibility throughout the IT asset lifecycle.
Conclusion
AI has redefined ITAD, transforming it from a behind-the-scenes operational task into a critical component of cybersecurity strategy. Today, end-of-life devices are managed with the same level of scrutiny as active endpoints, shifting the focus from simple waste disposal to a proactive, intelligence-driven approach to asset management. Considering the average cost of a data breach in the U.S. has soared to $10.22 million, relying on outdated, manual methods for data sanitization and compliance is no longer a viable option.
The numbers speak volumes: 95% of security decision-makers say AI and automation have enhanced their teams' effectiveness, with 51% reporting faster risk assessments and 50% noting improved accuracy in their security measures. These advancements are essential as global e-waste is projected to hit 82 million metric tons by 2030. At the same time, modern AI hardware like GPUs, TPUs, and NPUs introduces sanitization challenges that traditional methods simply can't handle.
ITAD expert George Ganas sums up this transformation succinctly:
"AI is turning ITAD into a proactive, intelligence-led function rather than a reactive one - reducing loss, maximizing recovery, and improving compliance accuracy".
AI-powered ITAD solutions offer real-time asset tracking, automated alerts for anomalies, and cryptographic proof of destruction. By moving away from manual, screenshot-based documentation to automated systems, organizations can eliminate performative "security theater" and focus on addressing real risks.
Rica Recycling is a prime example of this evolution, integrating AI-enhanced ITAD services with certified data destruction practices, compliance with California's e-waste regulations, and a commitment to environmental responsibility. By adopting AI-driven ITAD, organizations can meet today's data protection demands while preparing for the challenges of tomorrow.
FAQs
How does AI verify data wiping is complete?
AI uses specialized software to permanently erase data, ensuring it cannot be recovered. This process also generates compliance certificates, which verify that the data wiping meets established security standards. These certificates provide proof of secure data destruction and help organizations comply with privacy regulations.
What makes AI servers and GPUs harder to sanitize?
AI servers and GPUs come with unique challenges when it comes to sanitization. Their higher cost and greater complexity mean that proper disposal isn't as straightforward as with standard IT equipment. Additionally, these devices often house sensitive data, making data security a top priority during disposal. On top of that, many AI hardware components contain hazardous materials, requiring careful handling to ensure safety and compliance with regulations. These factors combine to make managing AI hardware significantly more demanding.
What is cryptographic proof of destruction?
Cryptographic proof of destruction, also known as cryptographic erasure, is a method to ensure data becomes permanently inaccessible. This is achieved by keeping the data encrypted and then destroying the encryption keys. Without these keys, recovering the encrypted data is impossible, making it a secure approach to data destruction.
