Reverse Logistics for ITAD: Best Practices
Reverse logistics for IT Asset Disposition (ITAD) is the process of securely transporting retired IT equipment back to facilities for value recovery or proper disposal. It’s not just about moving hardware; it’s about protecting sensitive data, complying with strict regulations, and maximizing financial returns. Here’s what you need to know:
- Why It Matters: Data breaches cost an average of $4.45 million per incident, and devices lose resale value quickly - 2–4% per month after four years of use. A strong system ensures security, compliance, and cost savings.
- Key Challenges: Safeguarding data, managing logistics for remote or decentralized offices, and avoiding unnecessary destruction of reusable devices.
- Core Steps:
- Collection & Transportation: Secure tagging, GPS tracking, and tamper-proof materials.
- Value Recovery: Prioritize resale, redeployment, and electronic recycling to recover up to 40% of an asset's value.
- Data Destruction: Follow NIST SP 800-88 standards and work with certified partners like R2v3 or e-Stewards.
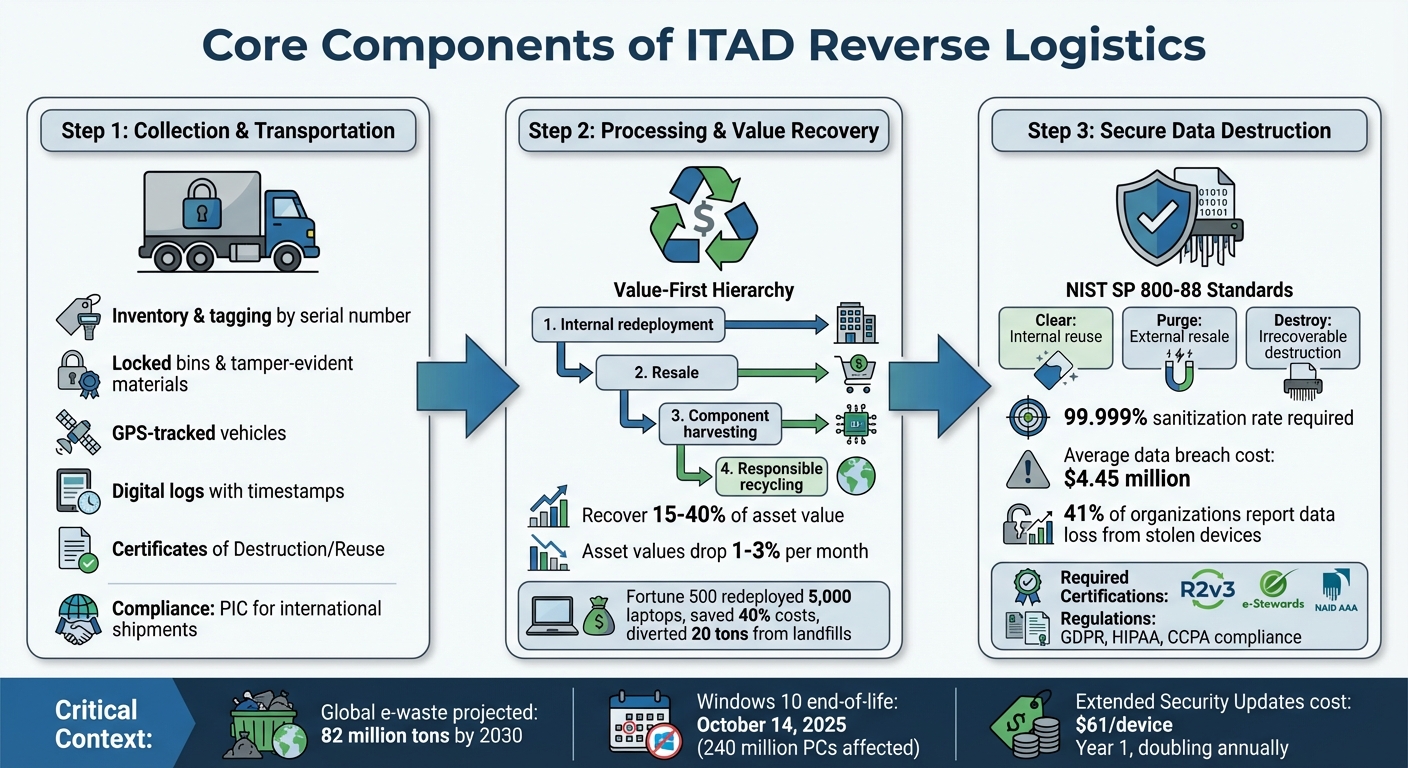
With global e-waste projected to hit 82 million tons by 2030, companies must focus on proper ITAD practices to save costs, reduce risks, and meet regulatory requirements. The end-of-life for Windows 10 in October 2025, for instance, will drive a surge in ITAD activity - planning ahead is critical.
ITAD February Webinar: How ITADs Win or Lose Enterprise Business with Reverse Logistics
sbb-itb-855056e
Core Components of Reverse Logistics for ITAD
ITAD Reverse Logistics: 3-Step Process for Secure IT Asset Disposition
A well-designed reverse logistics system for ITAD revolves around three main pillars: collection and transportation, processing and value recovery, and secure data destruction. Each step requires specific protocols and expertise to ensure maximum value recovery and compliance. Let’s break down these critical components.
Collection and Transportation
The process begins with inventory and tagging. Each device is logged by serial number and tagged to ensure traceability from the moment it’s decommissioned until its final disposition. This step is crucial for maintaining accountability and avoiding the risk of losing assets in the process.
To safeguard devices during transit, use locked bins and tamper-evident materials. This approach protects against both physical damage and unauthorized access. High-security transportation methods often include GPS-tracked vehicles, sealed containers, and trained personnel who understand the sensitive nature of the cargo. Digital logs with detailed timestamps, signatures, and handoff records further enhance transparency.
For international shipments, compliance with the Principles for International Cooperation (PIC) is essential. Additionally, obtaining a Certificate of Destruction or Certificate of Reuse with serial-level verification ensures accountability and adherence to global standards.
Processing and Value Recovery
Once devices reach the processing facility, they follow a value-first hierarchy. This means prioritizing internal redeployment, followed by resale, component harvesting, and finally responsible recycling. This approach not only boosts financial returns but also reduces environmental impact. Resale and remarketing can be especially lucrative, with organizations often recovering 15% to 40% of an asset’s value.
For example, in 2024, a Fortune 500 company redeployed over 5,000 laptops from its returned devices. This initiative slashed acquisition costs by 40% and kept more than 20 tons of e-waste out of landfills. Achieving such results requires a thorough assessment of components like processors, storage, and displays to determine the most cost-effective options.
Timely processing is critical - asset values typically drop by 1% to 3% each month. To avoid unnecessary depreciation, coordinate with your ITAD partner before major technology refreshes. This is especially important as the October 14, 2025, end-of-life date for Windows 10 approaches. The event is expected to drive a surge in ITAD activity, impacting an estimated 240 million PCs globally. Delays in disposition could result in costly Extended Security Updates, starting at $61 per device in the first year and doubling annually.
Once the value of the assets has been maximized, the focus shifts to data security.
Secure Data Destruction
Data security is non-negotiable in ITAD. With the average cost of a data breach reaching $4.45 million and 41% of organizations reporting data loss from stolen devices, robust sanitization measures are a must.
"Effective IT asset disposal is not just a regulatory necessity; it's a strategic approach to managing business risks and sustainability."
- Jesse Degroot, Vice President of Operations, UCS Logistics
Follow NIST SP 800-88 guidelines for sanitization: use Clear methods for internal reuse, Purge for external resale, and Destroy for irrecoverable destruction. Strive for a sanitization rate of 99.999%, and if drives are physically damaged, ensure they’re destroyed entirely. Work exclusively with partners certified by R2v3, e-Stewards, or NAID AAA. These certifications also help with compliance under GDPR, HIPAA, and CCPA regulations.
Companies like Rica Recycling (https://ricarecycling.com) offer secure data destruction as part of their ITAD services. They provide certificates that document each device’s serial number, data status, and final disposition. This level of transparency not only protects organizations but also supports a circular economy by making IT assets safe for reuse and resale.
Best Practices for ITAD Reverse Logistics
Handling ITAD reverse logistics effectively requires strategies that prioritize efficiency, data security, and compliance with environmental standards. With the global ITAD market expected to grow from $25.31 billion to approximately $54.54 billion by 2030, organizations must adopt reliable practices to safeguard data, recover value, and adhere to regulations.
Improving Asset Collection Processes
A strong foundation for ITAD reverse logistics begins with a verified inventory of assets. Using standardized tagging methods like barcodes or RFID, along with digital chain-of-custody logs, ensures accurate tracking from the moment assets are decommissioned to their final destination. Assigning an internal lead, such as an IT or Compliance Manager, to oversee the process helps ensure that asset counts align with internal inventories.
To avoid issues down the line, implement a pre-disposal checklist. This should include steps like removing user credentials, verifying backups, and flagging items that require enhanced destruction before they leave your facility. These measures not only reduce the risk of assets going missing but also address potential data breaches, which can cost an average of $4.45 million per incident.
Using Technology in Reverse Logistics
Technology can take ITAD reverse logistics to the next level. Modern ITAD ERP systems streamline operations by offering real-time visibility and automating tasks like certificate generation. This reduces manual errors and speeds up the sorting of assets into repair, resale, or recycling categories. Considering that $744 billion worth of products were returned in the U.S. in 2023, the role of technology in improving efficiency is clear.
Automating inventory syncing is another key step. By connecting surplus asset lists directly to ITSM or CMDB exports, you can ensure accuracy before the reverse logistics process begins. Additionally, AI and machine learning tools can analyze the condition, demand, and resale value of returned items to determine whether they should be refurbished, harvested for parts, or recycled.
For data sanitization, adopt a risk-based approach. High-risk devices like government servers may need multi-pass wiping combined with degaussing or physical destruction, while lower-risk IoT devices might only require a quick wipe and account unlinking. Certified tools like Blancco or KillDisk can automate data destruction to meet NIST SP 800-88 standards, providing detailed logs of the process.
Client portals are another valuable tool. They offer real-time tracking of assets and instant access to destruction certificates. This level of transparency builds trust, eases administrative tasks, and ensures compliance with upcoming regulations like the Basel Convention's Prior Informed Consent (PIC) requirements for cross-border e-waste shipments, effective January 1, 2025.
Working with Certified Recycling Partners
Technology is most effective when paired with certified partners who uphold strict environmental and compliance standards. Collaborate with ITAD providers that are certified under programs like R2v3 or e-Stewards to ensure responsible handling of hazardous materials such as batteries and mercury-containing displays.
When choosing a provider, verify the scope of their certification to ensure it aligns with your needs. Request a summary of their downstream due diligence to confirm how and where hazardous components are processed. With the Basel Convention's new rules requiring PIC for cross-border e-waste shipments starting in 2025, working with certified partners is more important than ever.
To maintain a closed-loop chain of custody, demand serialized reporting that tracks each device from collection to its final disposition. Additionally, establish strict Service Level Agreements (SLAs) that include specific timelines, such as receiving Certificates of Destruction within 48 hours of facility intake.
For example, Rica Recycling provides certified electronics recycling and ITAD services, offering secure data destruction and Certificates of Destruction for every device they process. With a 100% landfill-free policy, they comply with California’s e-waste regulations while helping organizations meet sustainability goals. Their serialized tracking and certified processes also help mitigate the financial and reputational risks of data breaches, which average $4.45 million per incident.
Compliance and Environmental Responsibility in ITAD Reverse Logistics
California E-Waste Regulations and Compliance
California has some of the strictest e-waste regulations in the United States, directly impacting IT asset recovery practices. If your business handles off-site e-waste, you’re required to file a Notice of Intent (NOI) with the Department of Toxic Substances Control (DTSC) at least 30 days before starting operations. This rule applies to handlers, collectors, and recyclers working within the state.
In addition, facilities must submit annual reports by February 1 if they surpass thresholds set for generators, collectors, or recyclers. Missing these deadlines can lead to penalties and disrupt your reverse logistics processes.
Another key requirement: all personnel managing electronic devices must complete initial training and annual refresher courses. These sessions cover topics like hazard recognition, proper handling techniques, and emergency protocols.
Planning to export electronic devices or CRT glass for recycling? You’ll need to notify the DTSC at least 60 days in advance. These detailed regulations are designed to ensure responsible IT asset disposition (ITAD) practices, aligning with California’s environmental goals.
Environmental Benefits of 100% Landfill-Free Policies
Adopting a landfill-free ITAD policy can significantly reduce the environmental harm caused by electronic waste. Electronics often contain hazardous substances like lead, mercury, cadmium, and arsenic, which can seep into soil and groundwater, posing risks like cancer and neurological issues. With global e-waste reaching 62 million tonnes in 2022 and projected to hit 82 million tonnes by 2030, the need for responsible disposal has never been more pressing.
“Data is a toxic asset, and saving it is dangerous.” - Bruce Schneier, Security Expert
To ensure transparency and accountability, serial-level tracking is essential. It documents the journey of each device from collection to its final destination, closing audit gaps and supporting environmental claims. Certifications like "Zero Waste to Landfill" provide independent verification through audits, proving that e-waste is diverted away from landfills.
Companies like Rica Recycling have embraced a 100% landfill-free policy, processing all electronics through certified channels. This approach not only helps Bay Area businesses comply with California’s strict environmental standards but also aligns with broader sustainability goals. By partnering with certified providers who maintain audit trails, organizations can demonstrate compliance, reduce their environmental impact, and enhance the value recovery process in ITAD. These practices protect public health while reinforcing responsible asset management.
Auditing and Certifications for ITAD
Certifications such as R2 (Responsible Recycling) ensure that ITAD providers adhere to stringent environmental and security standards. These certifications require regular audits, detailed documentation, and verified downstream disposal processes. Without certification, businesses risk jeopardizing both data security and environmental compliance.
To stay audit-ready, maintain detailed chain-of-custody logs that track each asset from removal to final disposal. This documentation is especially critical in California, where regulators demand thorough records during compliance reviews. Certifications like R2 not only uphold environmental standards but also safeguard sensitive data, emphasizing the importance of responsible ITAD practices.
When disposing of assets, always request a Certificate of Destruction that includes specific serial numbers rather than vague batch details. California auditors require this level of precision to confirm proper handling. Generic certificates stating “X number of devices destroyed” won’t meet regulatory expectations or provide the accountability needed to demonstrate compliance. Rigorous documentation and certifications are key to maintaining trust and meeting environmental and security standards in ITAD operations.
Building an Effective ITAD Reverse Logistics Program
Key Takeaways
Creating a strong ITAD reverse logistics program begins with thorough asset documentation. Start with a detailed hardware audit that records each device's specifications, age, and condition. This inventory becomes the backbone of your strategy, helping you identify opportunities to recover value.
Data security should be a top priority. Before any device leaves your facility, follow NIST 800-88 sanitization protocols to ensure all data is securely wiped. With data breaches costing an average of $4.45 million, proper data destruction isn't just smart - it's essential. Additionally, remove company logos and internal asset tags from retired equipment to prevent unauthorized use or identification.
To maximize value recovery, adopt a tiered approach: redeploy usable assets internally, then focus on reselling, harvesting components, and finally recycling. Well-developed programs can deliver impressive results, with some achieving a 20:1 value-leverage ratio - turning $100,000 in disposal costs into $2 million in remarketing value.
Audit readiness is another critical factor. Maintain serial-level tracking from the moment assets are decommissioned through final disposition. Secure Certificates of Destruction that include serial numbers to ensure compliance. Partnering with certified providers - those holding R2v3, e-Stewards, or NAID AAA credentials - guarantees adherence to both environmental and data security standards.
These strategies lay the groundwork for actionable improvements to your ITAD program.
Next Steps for Businesses and Organizations
To take your ITAD reverse logistics to the next level, start by mapping your existing IT assets and identifying devices nearing the end of their lifecycle. This is especially important with upcoming changes like the end of Windows 10 support on October 14, 2025, which affects an estimated 240 million PCs worldwide. Delaying action could get costly - Extended Security Updates start at $61 per device in Year 1 but skyrocket to $244 by Year 3. Planning ahead can save significant money.
Work with a certified ITAD provider that understands state-specific regulations, particularly if you’re in California. For instance, Rica Recycling provides certified electronics recycling and IT asset recovery services in the San Francisco Bay Area. Their 100% landfill-free policy ensures compliance with California's strict e-waste regulations. Services include secure data destruction with certificates, convenient pickup options, and a focus on turning liabilities into responsible solutions - all while ensuring both data and environmental security.
FAQs
What devices need “Clear” vs “Purge” vs “Destroy” under NIST 800-88?
Under NIST 800-88, data sanitization is categorized into three levels based on the sensitivity of the data and the required method of disposal:
- Clear: This method is used for devices containing non-sensitive data. It typically involves overwriting the data to make it unrecoverable through standard software-based techniques.
- Purge: Designed for highly sensitive data, this approach uses more advanced methods such as cryptographic erasure or degaussing to ensure data cannot be retrieved.
- Destroy: For critical or classified data, physical destruction methods like shredding are employed. This level is necessary when software-based solutions are inadequate or when regulations mandate physical destruction.
Each level ensures data is handled appropriately based on its sensitivity and regulatory requirements.
How do I prove chain of custody from pickup to final disposition?
To establish a clear chain of custody, it's essential to maintain a detailed record that tracks every step of an asset's journey. This includes logging serial numbers, documenting custody transfers, noting transport details, and recording the final disposition of the asset.
Use tools like tamper-evident seals, photographs, and signed logs at each transfer point to ensure accountability. Creating a standard operating procedure (SOP) with clearly assigned roles for intake, transport, and documentation is equally important.
Working with a certified ITAD provider adds an extra layer of assurance by providing traceable, audit-ready documentation throughout the entire process.
How early should we schedule ITAD before the Windows 10 end-of-support date?
Planning your IT asset disposition (ITAD) ahead of Windows 10's end-of-support date - October 14, 2025 - is a smart move. Starting early ensures secure data disposal, compliance with regulations, and avoids the chaos of last-minute decisions that could lead to mistakes or extra expenses. By acting now, you can make the process smoother while prioritizing both data security and environmentally responsible practices.
